If you have used the same phone number for more than three years, the answer is almost certainly yes.
In 2026, most active numbers have been exposed in at least one public breach or scraped by data brokers.
The critical question now isn’t whether your number is on a list, but whether that exposure puts your bank accounts and identity at immediate risk.
Table of Contents
Has My Phone Number Been Leaked? (Is My Phone Number Leaked)
It is crucial to understand that a leaked number is simply listed in a database, while a hijacked number is actively being used by criminals to intercept your calls and texts.
Being leaked does not mean you have been hacked yet, but it does make you a visible target for future scams.
Checking your status helps you decide if you can simply ignore spam or if you need to immediately lock down your financial accounts.
The next step is to confirm exactly which databases contain your number so you can assess your true risk level.
How to Check If Your Phone Number Is in a Data Breach
Since no single tool indexes every dark web leak and data broker list, you must use a combination of methods to fully confirm your exposure.
Have I Been Pwned: Phone Number Data Breach Check
Have I Been Pwned (HIBP) is the most trusted service for checking exposure, specifically scanning billions of records from massive, publicly verified data breaches.
However, because this tool does not index data broker databases or scraped public profiles, a clean result does not guarantee your number is completely private.
What Does It Mean If Your Phone Number Is Leaked?
When your phone number is “leaked,” it simply means that your digits, often linked to your name or email, have been added to a database accessible to unauthorized parties.
In most cases, this does not mean your actual phone has been hacked or that criminals are listening to your calls.
Instead, it usually means your information was “scraped” from public social media profiles or aggregated by data brokers who legally collect and sell user information.
The reality is that once a number enters these databases, it effectively becomes public record. Unlike a password which can be changed to stop access, a leaked phone number is a “static” identifier that persists indefinitely.
While this exposure doesn’t always lead to immediate theft, it permanently connects your online accounts to your real-world identity, making you reachable by spammers and scammers.
What Happens When a Phone Number Is Leaked?
The most immediate consequence is a noticeable increase in automated spam.
Leaked lists are frequently sold to marketing firms and scam networks, resulting in a wave of robocalls and “smishing” texts designed to trick you into clicking malicious links.
Beyond generic annoyance, this exposure enables targeted “vishing” attacks, where scammers use your leaked name and personal details to impersonate banks or government officials, building trust before asking for sensitive information.
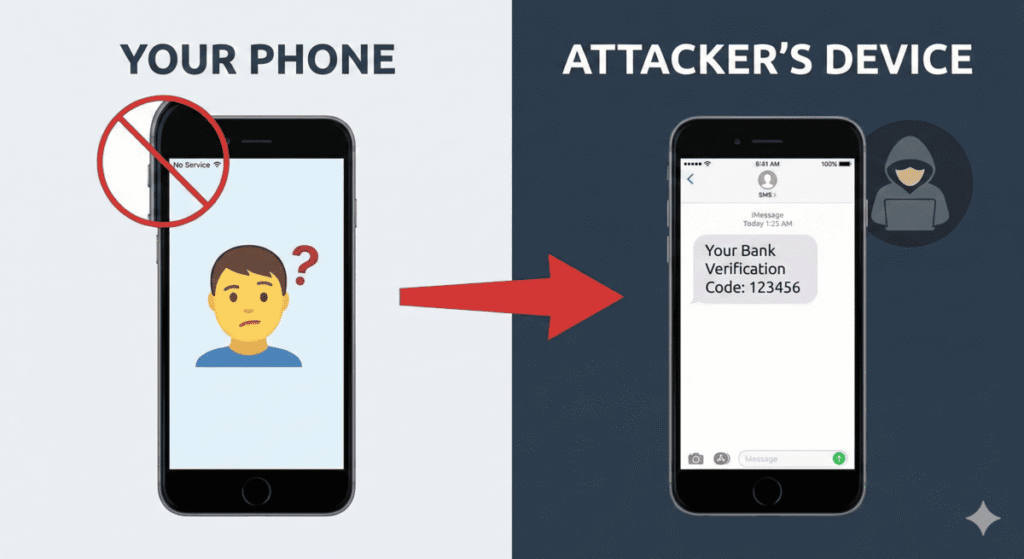
A more serious risk involves SIM swapping. With your phone number and personal details exposed, a determined criminal might attempt to trick your carrier into transferring your service to their device, allowing them to intercept your calls and text messages.
Finally, because many services still use phone numbers for identity verification, attackers can potentially use a compromised number to trigger password resets or bypass security questions on your other online accounts.
What to Do If Your Phone Number Was Leaked?
The first priority is to secure your primary email and banking accounts. Since phone numbers are often used for account recovery, a leak puts these essential services at risk.
Ensure you have strong, unique passwords for these accounts and review your security settings to verify no unauthorized recovery methods have been added by an intruder.
Next, you should systematically remove SMS-based two-factor authentication from your security protocols. Relying on text messages for login codes is risky because if your number is intercepted, the attacker gets your codes.
Switch to using an authenticator app or hardware security key, which generates codes locally on your device and cannot be intercepted through the cellular network.
Finally, contact your mobile carrier to establish a port-out PIN or transfer lock. This is a specific security code that must be provided before your phone number can be moved to a new SIM card or a different carrier.
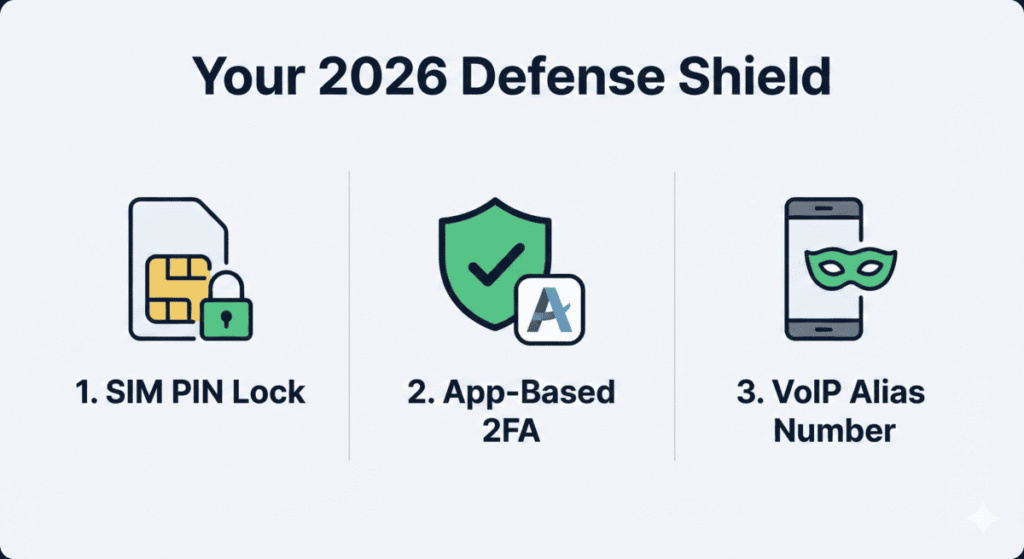
Adding this layer makes it significantly harder for criminals to perform a SIM swap attack, even if they have all your other personal information.
Can You Prevent Future Phone Number Leaks?
While you cannot prevent a company you trust from suffering a data breach, you can significantly reduce your exposure by limiting who has your real phone number in the first place.
The most effective strategy is data minimization: before typing your digits into a form, pause and ask if that service truly requires your personal cell number or if email would suffice.
For non-essential services like delivery apps, newsletters, or one-time signups, consider using a secondary alias number or a VoIP service.
This keeps your primary number private and reserved only for banks, family, and critical accounts. You can also improve privacy on messaging apps by taking steps to hide your phone number on Telegram so it isn’t visible to strangers.
Finally, regularly audit your app permissions. Many mobile apps request access to your contacts or phone status unnecessarily; revoking these permissions stops them from scraping your data.
Should You Change Your Phone Number?
For most people, the answer is no. Changing your phone number is rarely the right solution and often creates more problems than it solves.
Telecom providers recycle phone numbers rapidly, meaning a “new” number typically comes with the previous owner’s spam history, debt collection calls, and data breach footprint. You often end up trading a known problem for an unknown, potentially worse one.
Furthermore, updating your number across every bank, government service, and social account is a logistical nightmare that risks locking you out of your own digital life if a 2FA code is sent to the old line.
Unless you are the victim of persistent, targeted harassment that cannot be blocked, the smarter strategy is to “insulate” your current number.
By adding a carrier PIN and moving 2FA to apps, you secure the line against attacks without the massive disruption of changing your identity.
FAQ
What is a phone number breach?
A phone number breach occurs when your number is exposed to unauthorized parties, either through a direct hack of a company’s database or through “scraping” public profiles. Unlike a password breach, a phone number breach links your digital identity to your real-world identity, making you a target for phishing and spam.
Has my phone number been leaked?
You can confirm if your number has been leaked using databases like Have I Been Pwned. However, if you have used the same phone number for more than three years, it is statistically likely that it has already appeared in a breach or data broker list.
Can my phone number be hacked?
Technically, a phone number is not “hacked” like a computer; it is hijacked. The primary threat is a SIM Swap Attack, where a criminal tricks your carrier into transferring your service to their SIM card. If successful, they receive your calls and 2FA codes while your phone loses service.
Should I change my phone number after a data breach?
Rarely. In most cases, changing your number creates more problems than it solves because telecom providers recycle numbers quickly. Unless you are being actively targeted by a persistent threat, it is better to insulate your current number using a carrier PIN and app-based 2FA rather than changing it.